IIS 6.0 setup on Windows Server 2003 R2
-
IIS Services (Core component Services)
-
Web Server
- Virtual Directory
- Virtual Server: related closely with DNS
-
Using HTTP/HTTPS Protocols
- TCP/IP (Port & Address)
- Default Web Server Port: 80
-
FTP (File Transfer Protocol)
- Default Access port:21
-
SMTP/POP3
- Simple Mail Transfer Protocol: Communication protocol between two MTA (Mail Transfer Agent) Servers
-
Post Office Protocol 3: Communication protocol from a mail Server to a client
- IMAP (another type of receiving client protocol)
- NNTP (Network News Transfer Protocol) – intranet and news group protocol
-
Terminal Service Remote Desktop
- Able to access with a Web Browser (IE)
-
-
TCP Ports and Protocols (Default)

Install IIS Service
-
On websvr1, open Manage Your Server>Add or Remove a Role

-
Next

-
Select Application Server (IIS)

-
Next

-
Finish

-
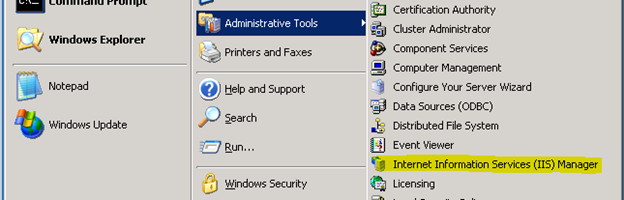
Open IIS Manager
Build Out Web Server
-
On DC1>DNS Manager, create a CNAME www and map to websvr1.vmlab.local

Setup a root CA on websvr1
-
Install Certificate Services




-
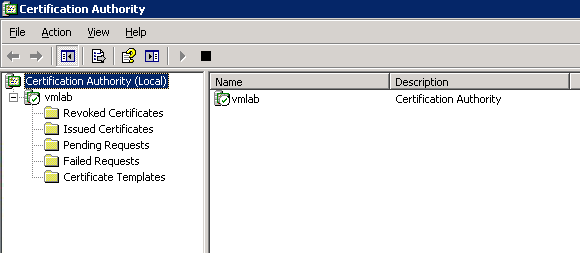
Administrative Tools>Certification Authority

-
CA MMC
-
On IE, go to http://websvr1/certsrv/ and input credentials

-
Certificate Service Site should be loaded

-
Check CRL share properly or not. Open Run> type \\websvr1\Certenroll\

-
It works

Build out SubCA
- Typically, for the security reason, we’d better have a sub CA to create a new server certificate not from Root CA.
- Deploy another Windows server 2003 R2 and name it subca for setup sub CA and test out
-
Install Certificate Services on this server as well







-
Install IIS service to use Sub CA server serivce



Obtain a Server Certificate
- Back to IIS console on websvr1
-
On Default Web Site>Properties>Directory Security>server certificate

-
Next


-
Select Send the request immediately to an online certificate authority









-
Click View Certificate



-
Click Edit to set require to use secure channel (SSL) for communication from a client to this server


-
Test with http://www.vmlab.local on IE , but it will generate an error to display

-
Test again with https://www.vmlab.local and it should work as below




EFS (Encrypting File System)
Recreate Recovery agent
-
Open Group Policy Management and Edit Default Domain Policy>Computer Policies>Windows Settings>Security Settings>Public Key Policies>Encrypting File System

-
The Certificate for Administrator status is not trusted since it was built in

-
Its intended purpose is for File Recovery

-
Delete built in Administrator recovery agent cert

-
Right click on Encrypting File System >Create Data Recovery Agent

-
New recovery agent is created

-
The certificate status Is ok


Test EFS
-
Right click the target file and properties> Under General Tab>Advanced

-
Check Encrypt Contents to secure data (It supposes not to be compressed to apply EFS- which color scheme is blue)

-
Select Encrypt the file only

-
The file color scheme is changed to Green and attribute to AE as well

-
Go to the properties>Advanced> Details

-
Data Recovery Agent for the file as defined by policy
